Delivery vs. Discovery: The Future of Digital Secrets
One method sends a high-tech envelope; the other simply knows the secret like telepathy. A deep dive into the math defining the next decade of privacy.
Before we dive into the “Ghost” architecture, we need to define the two players changing the way we lock our data. In 2026, the world of cryptography has split into two distinct philosophies: KEM and NIKE.
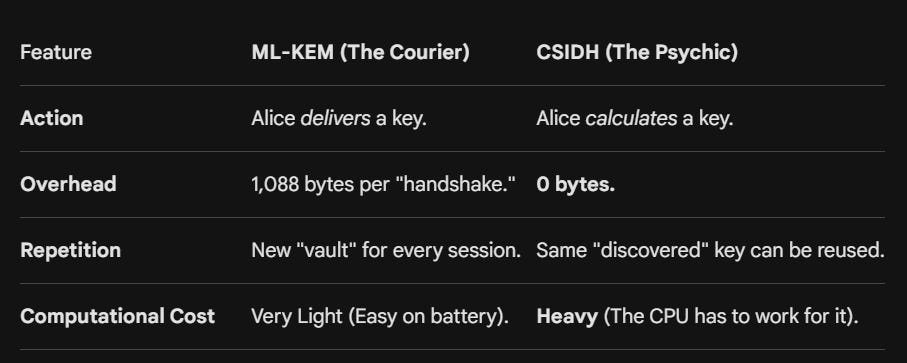
KEM (Key Encapsulation Mechanism): Think of this as the “Delivery.” It is a method where one person creates a secret key, encapsulates (locks) it in a digital vault, and delivers it to the recipient. It is the new global standard for speed and efficiency.
NIKE (Non-Interactive Key Exchange): Think of this as the “Mind Reader.” It is a method where two people can arrive at the same secret key independently without ever speaking to each other or sending a vault. There is no interaction required, just pure mathematical discovery.
The “Ghost” Architecture: KEM vs. NIKE
Both of these look one-way. Alice sends a file, and Bob opens it later. But under the hood, the way they handle the secret is fundamentally different.
ML-KEM: The One-Way Key Transport Delivery
Think of ML-KEM (the NIST standard) as a high-tech delivery service.
The Process: Alice generates a fresh secret key. She puts it inside a quantum-resistant vault (the encapsulation) and sends that vault to Bob.
The Reality: Even though Bob doesn’t have to be online, Alice must send the key to Bob. She is delivering the key to him. If Alice wants maximum security (Forward Secrecy) for 10 different files, she has to send 10 different vaults, but she could technically encapsulate one key and use it to encrypt all 10 files (a session key).
The Overhead: That vault adds about 1KB to every single file.
CSIDH: The Key Discovery
CSIDH (pronounced “sea-side”) is different. It’s a NIKE. In this world, the key isn’t delivered; it is discovered.
The Process: Alice looks at Bob’s public key. She doesn’t generate a new secret to send him. Instead, she uses her own private key and his public key to math her way to a shared secret. Bob does the same on his end.
The Reality: The key is already there in the math. Alice sends zero bytes of key data. She just sends the encrypted file.
The Efficiency: If Alice sends 10 files to Bob, she doesn’t need to send 10 vaults. They both already know the secret combination just by existing on the network. Plus, the "address" Bob leaves behind (his Public Key) is tiny at only about 64 bytes for CSIDH-512, compared to the much larger 1,184 bytes required for a standard ML-KEM-768 key.
What is Harvest Now Decrypt Later (HNDL)?
The greatest threat to privacy today isn’t a current hack; it’s a recording.
The Attack: State actors and adversaries are currently harvesting encrypted traffic from the wire. They can’t read it today, so they store it in massive data centers.
The Payoff: In the 2030s, when a Cryptographically Relevant Quantum Computer (CRQC) goes live, they run Shor’s Algorithm against that old traffic.
Why these are safe: Both CSIDH and ML-KEM rely on math (Isogenies and Lattices, respectively) that is safe from the known quantum attacks that currently break RSA and ECC like Shor’s Algorithm. Even with a quantum computer, the attacker is left staring at noise.
The Risk of the Wrong Wrapper: If you use a quantum wrapper that still relies on an initial classical handshake (like a standard ECDH exchange) to set up the tunnel, an attacker can harvest that initial handshake. Once they break the outer classical lock in the future, your inner 3-pass protocol is exposed.
Two Contenders
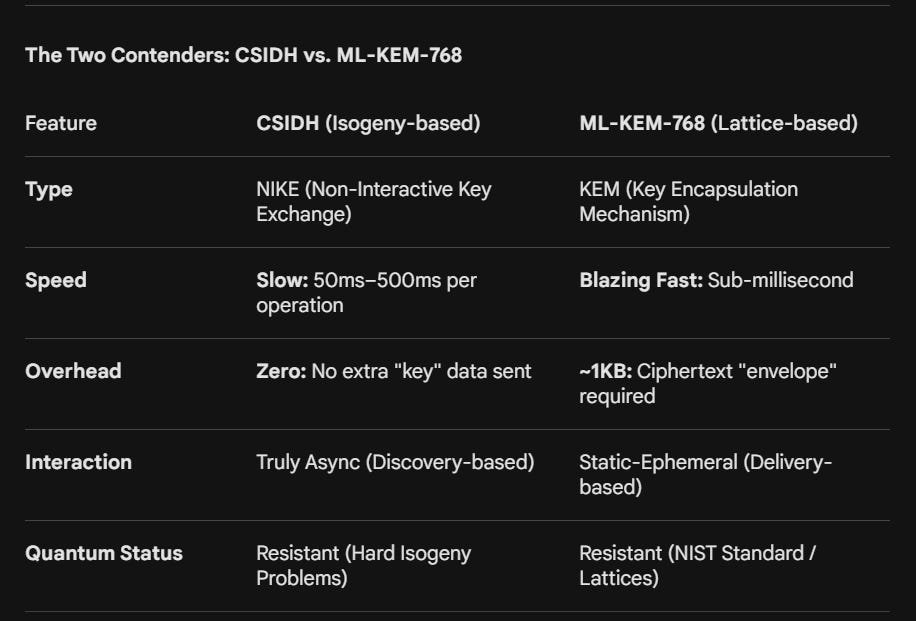
In the race to secure our decentralized systems against “Harvest Now, Decrypt Later” (HNDL) attacks, we’ve reached a fork in the road. Do we take the Fast Wrapper (ML-KEM) or the Elegant Pure-Path (CSIDH)?
Path A: The Hybrid “Quantum-Salt” Wrapper (Delivery)
This is the pragmatic 2026 choice. You take your classical 3-pass (Pohlig-Hellman) and wrap it in a layer of ML-KEM-768.
The Flow: Alice looks up Bob’s static public key, generates a secret, “encapsulates” it in a 1KB ML-KEM envelope, and sends it along with the file.
Pros: It’s incredibly fast. Your CPU won’t even blink.
Cons: You lose the “Pure Ghost” feel. Every message or file-drop carries a 1KB “tax.” For a 10MB file, it’s a rounding error. For a tiny metadata packet, the wrapper is bigger than the gift.
Path B: CSIDH, The “Pure Ghost” NIKE (Discovery)
If you want to stay pure, where the key is never sent and only discovered, CSIDH is your holy grail.
The Math: This is a NIKE. Because Isogeny math is commutative (like Pohlig-Hellman), Alice and Bob can arrive at the same shared secret independently.
The Flow: Alice sees Bob’s public key on the DAG. Because a CSIDH public key is so small (about the size of a short tweet), it fits perfectly into decentralized headers. She does some heavy math on her end and encrypts the file. Bob does the same heavy math later. Zero bytes of extra key-delivery data are ever sent over the wire.
The Trade-off: CSIDH is heavy computation that trades battery life and time for bandwidth and stealth. On a newer mobile device, it’s about a 200ms–500ms delay and older devices can go as high as multiple seconds that creates a noticeable “thunk” in the user experience.
Why the Discovery Model Wins for the Long Game
In a Pure Ghost system, we want to minimize what an observer can see.
In the KEM model, a sniffer sees a 1KB vault being sent. They know a key exchange is happening.
In the NIKE (CSIDH) model, the sniffer just sees data. There is no key transport to identify, no vault to track. It is the ultimate expression of digital sovereignty: the secret is never transmitted because the secret was never sent, it was calculated.
ML-KEM is like a Formula 1 car. It is blazing fast and lightweight on your battery, but you can see it coming down the track.
CSIDH is like a Submarine. It is heavy and moves slower (taking 200ms–500ms to calculate a key), but it moves in total silence beneath the surface.
A Note on the Hardware Path: Quantum 3-Pass
You may be wondering: “Why not just use a real Quantum 3-pass protocol?” While theoretically perfect, this requires Quantum Key Distribution (QKD). This isn’t software; it’s hardware. It requires dedicated fiber-optic lines or satellite lasers to maintain the quantum state of photons. For a decentralized game engine or a file-sharing app on a smartphone, QKD is currently a logistical impossibility. We use math (PQC) because we don’t have lasers in our pockets yet.
The Verdict for 2026
Use ML-KEM-768 if you value performance and don’t mind a 1KB “delivery tax” on every file. It’s the industrial strength solution that’s fast, standardized, and ready for high-traffic systems.
Use CSIDH if you are an architectural purist who demands zero-transport discovery. If you want to eliminate the overhead of sending keys entirely and can afford the CPU “weight,” this is your path.